They’re all dressed as politicians.
knightly the Sneptaur
- 0 Posts
- 39 Comments

 4·2 months ago
4·2 months agoDid they ever fire that cop?

 461·2 months ago
461·2 months agoAh, “Explaining”. There’s your problem.
Lets have a checklist with supporting documentation, please~

 101·2 months ago
101·2 months agoAs it should be.

 45·2 months ago
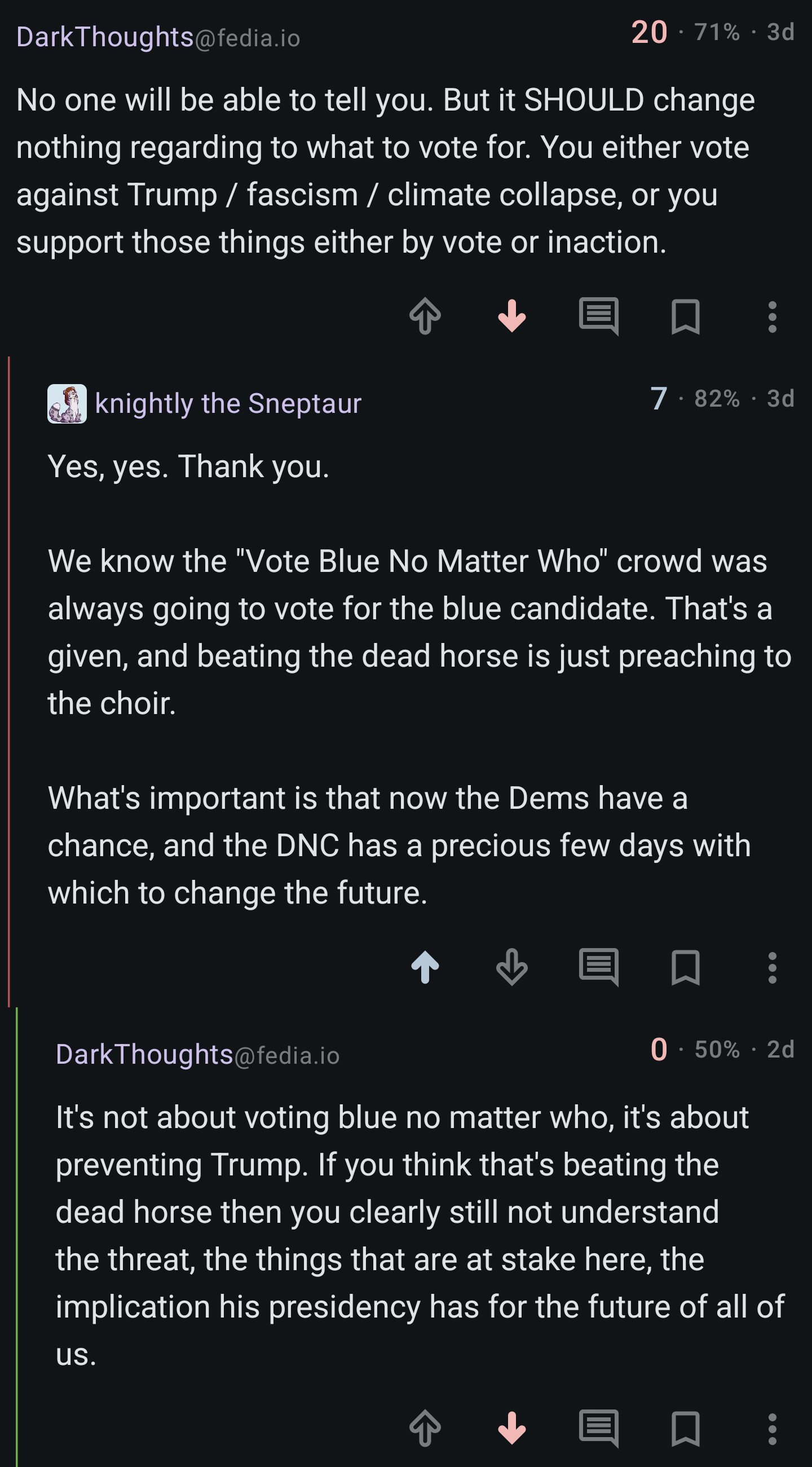
45·2 months agoJeeze, look at all the salty Bidenists giving you pissy downvotes now that their favorite big wet boy is planning for retirement.

I’ve been telling people that the Dems would have to drop the incumbent to win 2024 since 2016 when the DNC rigged their own primary, but no matter how I try to explain it I immediately get accused of being a Republican. I feel like Cassandra, cursed to utter true prophecies but never be believed.


 7·2 months ago
7·2 months agoNo matter how reasonably I phrase the argument, I haven’t been able to point out that the Dems would have better chances if Biden dropped out without getting accused of supporting Trump all the way up to the day after Biden dropped out.

 51·2 months ago
51·2 months agoIt shouldn’t be. Youtube could have been a public good but instead it’s for-profit.
You’re so close~
Voting is a placebo, but every election is stolen before it’s even held. Party members decide who gets to run in the primaries and draw the congressional districts to ensure no third parties could ever hope to win. Actual competition between the parties is limited to battleground states, electors elsewhere have no influence on the outcome.
So, you’re right, but not in the way you think. The political establishment pushes an illusion of choice to keep the population from exercising its power.
I have to go back over and stitch in the edges on all my iron-on patches, might have to look into that if they’ll do a better job.
I plan to, which pisses off Doctor Evil’s Democrats.

 103·4 months ago
103·4 months agoGood, get it all offline so the LLM Assholes can’t use it.
Queer folks have a bad habit of falling in love with people on the other side of the country.

 11·5 months ago
11·5 months agoThis but unironically.

 181·6 months ago
181·6 months agoAs long as you want, assuming that you’re fine with the security risks and everything that’s rendered incompatible in the future.

 41·6 months ago
41·6 months agoQuit ruining the joke. XD

 1513·6 months ago
1513·6 months agoSoftware companies don’t want you to know this, but the open-source licenses on the internet are free. You can just take them home. I have 458 apps.

 14·6 months ago
14·6 months agoA “side-channel attack” is one where fundamental flaws in the encryption implementation method are targeted, as opposed to flaws in the cryptographic algorithm itself.
By means of analogy, if your cryptographic method is to go to a locked room to have a private conversation, then a spy doesn’t have to pick the lock if they can still hear you through the door. The locked-room security method itself isn’t flawed, but implementing it without a soundproof door has much the same result.
In this case:
The threat resides in the chips’ data memory-dependent prefetcher, a hardware optimization that predicts the memory addresses of data that running code is likely to access in the near future. By loading the contents into the CPU cache before it’s actually needed, the DMP, as the feature is abbreviated, reduces latency between the main memory and the CPU, a common bottleneck in modern computing. DMPs are a relatively new phenomenon found only in M-series chips and Intel’s 13th-generation Raptor Lake microarchitecture, although older forms of prefetchers have been common for years.
Security experts have long known that classical prefetchers open a side channel that malicious processes can probe to obtain secret key material from cryptographic operations. This vulnerability is the result of the prefetchers making predictions based on previous access patterns, which can create changes in state that attackers can exploit to leak information.
So, the encryption the chips use is solid, but some of the hardware employed can still leak data.
Squats, I guess?

 3·6 months ago
3·6 months agoI want smaller games with worse graphics made by people who get paid a living wage to work reasonable hours and I’m not kidding.

Voting is the least important part of the political process. America is not a democracy, voting merely serves to legitimize the state with an illusion of choice.